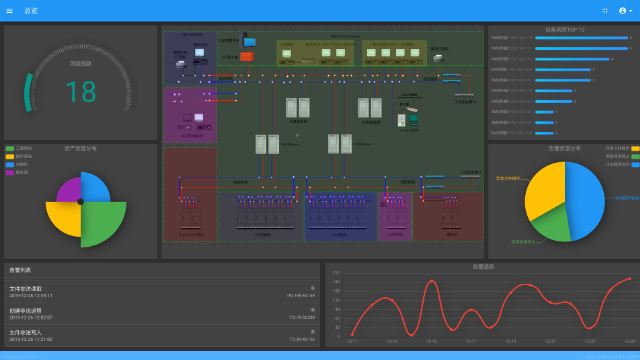
Unified monitoring and control of the industrial control system network security situation; trusted strategy management
Deep cultivation in the field of industrial control; knowledge base support for industrial control experts; network asset topology display in line with industrial control format
Fully independent security control; use of domestic commercial cryptographic algorithms using communication encryption and identity authentication technologies; industrial data security escort
Unified control of industrial network-based security devices fully meeting the requirements of the Cyber Security Technology — Baseline for Classified Protection of Cybersecurity 2.0 platform