The Asset Guarding System creates a trustworthy industrial control operating environment. It takes trusted computing technology as its core and builds upon Cyber Security Technology — Baseline for Classified Protection of Cybersecurity 2.0 with an integrated whitelist, mandatory access control, discretionary access control, peripheral management and other functions for an autonomous defense system able to resist attacks by unknown viruses, Trojans, and malicious codes.
Supports the trusted software base at the system kernel-level and realizes trusted kernel-layer metrics to ensure the security and credibility of the system execution environment; supports dynamic metrics of the running state to ensure business programs' operations process security
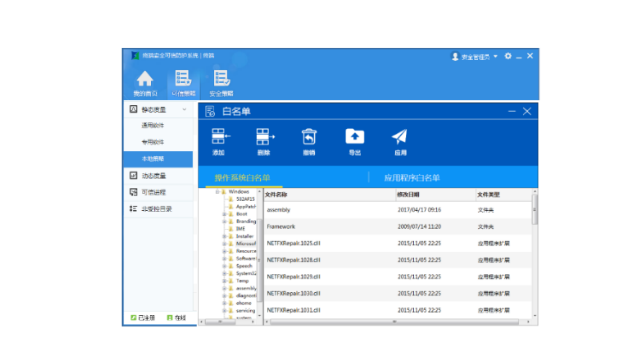
Supports B/S architecture centralized control; through the server-side, clients can realize complete unified configuration, key deployment, and centralized monitoring; strategy configuration supporting trusted computing, whitelisting, mandatory access control, discretionary access control and peripheral management
Supports operating system (OS) security reinforcement of host terminals with comprehensive OS behavior/event auditing functionality